In today's online landscape, cyberattacks are an ever-present threat. To secure your systems and data from these malicious actions, it is crucial to implement robust security measures.
A comprehensive information security strategy should encompass multiple layers of defense. This includes implementing strong passwords, employing multi-factor authentication, keeping software current, and training users on best practices for online safety.
- Moreover, it is important to monitor system activity for unusual behavior and configure intrusion detection and prevention systems.
- Regularly saving data is also essential to minimize the impact of a data breach.
- Via taking these precautions, you can significantly diminish the risk of becoming a target of a cyberattack.
Cybersecurity Best Practices: Fortifying Your Digital Defenses
In today's dynamic digital landscape, safeguarding your data and systems is paramount. Implementing robust cybersecurity best practices is essential for minimizing the risks of cyberattacks and protecting your valuable assets. A strong cybersecurity posture involves a multi-layered approach that includes various aspects, from implementing secure passwords to installing advanced threat detection systems.
- Regularly update your software and operating systems to patch vulnerabilities and protect against known threats.
- Turn on multi-factor authentication (MFA) for all critical accounts to add an extra layer of security.
- Inform yourself and your employees about common cybersecurity threats and best practices to promote a culture of security awareness.
- Track your network traffic for suspicious activity and integrate intrusion detection systems (IDS) to identify potential threats.
- Archive your data regularly to ensure you can recover in case of a ransomware attack or other data loss event.
By adhering to these cybersecurity best practices, you can significantly enhance your digital defenses and protect your organization from the ever-evolving threat landscape.
Stay Ahead of the Curve: Cybersecurity Best Practices
In today's interwoven world, safeguarding your information against cyber threats is paramount.
- Cybercriminals are constantly devising newcreative tactics to exploit vulnerabilities and steal sensitive data.
- Therefore, it's essential to adopt a proactive approach to digital safety. By implementing robust security measures, you can significantly minimize your risk of becoming a victim.
Strengthening Defenses: Techniques for Countering Cyber Attacks
In today's digital/online/virtual landscape, cyber attacks are an ever-present threat. Organizations of all sizes must proactively/rigorously/effectively implement robust security measures to safeguard/protect/defend their valuable assets and sensitive/confidential/private information. A multi-layered approach is essential, encompassing technical controls/measures/solutions, administrative policies/procedures/guidelines, and employee training/awareness/education.
- Implementing/Deploying/Establishing strong passwords and multi-factor authentication can significantly/drastically/substantially reduce the risk of unauthorized access.
- Regularly/Frequently/Consistently updating software and hardware/systems/devices patches is crucial to mitigate/address/counter known vulnerabilities.
- Educating/Training/Informing employees about common cyber threats and best practices can help prevent/avoid/stop phishing attacks and other social engineering schemes.
Implementing/Deploying/Establishing a comprehensive incident response plan is essential to quickly/efficiently/effectively contain and remediate any cyber security breaches. By taking these proactive steps, organizations can significantly/substantially/materially reduce their risk of falling victim to cyber attacks.
Keep Up With Trends : Essential Cybersecurity Tips
In today's online landscape, safeguarding your information is paramount. Attackers are constantly evolving their tactics, making it vital to keep up with trends and utilize robust read more cybersecurity protocols.
A strong framework for cybersecurity involves several key actions:
* Regularly update your software and platforms.
* Use complex passwords and enable multi-factor authentication.
* Be aware of phishing emails and avoid clicking on suspicious links.
* Save copies your data regularly to mitigate the impact of a breach.
Erecting an Impenetrable Firewall: Preventing Cyber Intrusions
In today's digital landscape, protecting your systems against hostile actors is paramount. A robust firewall acts as the first line of security, screening incoming and outgoing data to thwart threats. To truly achieve an impenetrable firewall, a multi-layered approach is necessary. This includes implementing state-of-the-art hardware, configuring firewall rules meticulously, and regularly patching your systems to reduce emerging threats.
- Furthermore, performing regular security assessments can reveal vulnerabilities and strengthen your overall security posture. Remember, a proactive approach to firewall administration is the key to effectively defending your network from cyberthreats.
 Michael J. Fox Then & Now!
Michael J. Fox Then & Now! Sam Woods Then & Now!
Sam Woods Then & Now!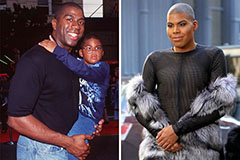 Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Tina Majorino Then & Now!
Tina Majorino Then & Now! Dawn Wells Then & Now!
Dawn Wells Then & Now!